Inside Intelligence Center: Financially Motivated Chinese Threat Actor SilkSpecter Targeting Black Friday Shoppers
In early October 2024, EclecticIQ analysts uncovered a phishing campaign that targets e-commerce shoppers in Europe and USA, looking for Black Friday discounts. Analysts assess with high confidence that it was very likely orchestrated by a Chinese financially motivated threat actor, analysts dubbed as SilkSpecter. The campaign leveraged the heightened online shopping activity in November, the peak season for Black Friday discounts. The threat actor used fake discounted products as phishing lures to deceive victims into providing their Cardholder Data (CHD) [1] and Sensitive Authentication Data (SAD) [2] and Personally Identifiable Information (PII).
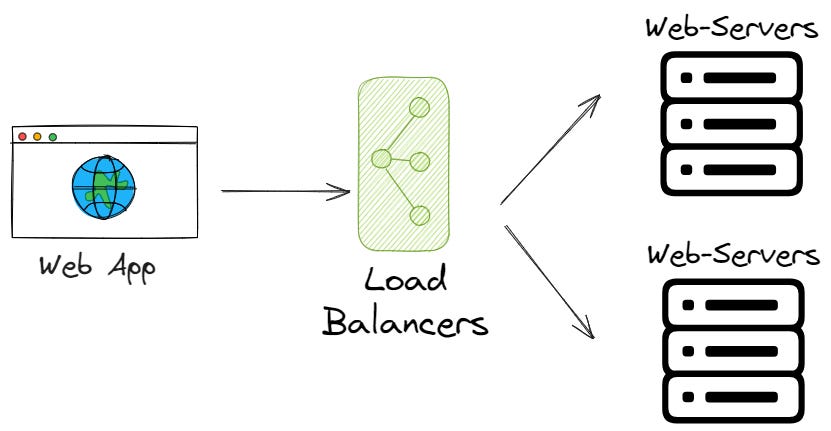
Threat actor SilkSpecter targeted victims' Cardholder Data (CHD) by leveraging the legitimate payment processor Stripe [3]. This tactic allowed genuine transactions to be completed while covertly exfiltrating sensitive CHD to a server controlled by the attackers. SilkSpecter enhanced the phishing site’s credibility by using Google Translate to dynamically adjust the website's language based on each victim’s IP location, making it appear more convincing to an international audience.
EclecticIQ analysts observed that prior to November 2024, SilkSpecter had launched similar phishing campaigns, all linked to a Chinese Software as a Service (SaaS) platform named oemapps [4]. Analysts assess with high confidence that oemapps very likely enables SilkSpecter to quickly create convincing fake e-commerce sites targeting unsuspecting users. These phishing domains predominantly use the .top, .shop, .store, and .vip top-level domains (TLDs), often typosquatting legitimate e-commerce organizations' domain names to deceive victims.













:focal(0x0:6000x4000)/static.texastribune.org/media/files/986e2fd2ae16eb6d1dd2993338a558a3/0928%20Cornudas%20Cookoff%20JH%2003.jpg)