SkyLift - Adam Harvey Studio
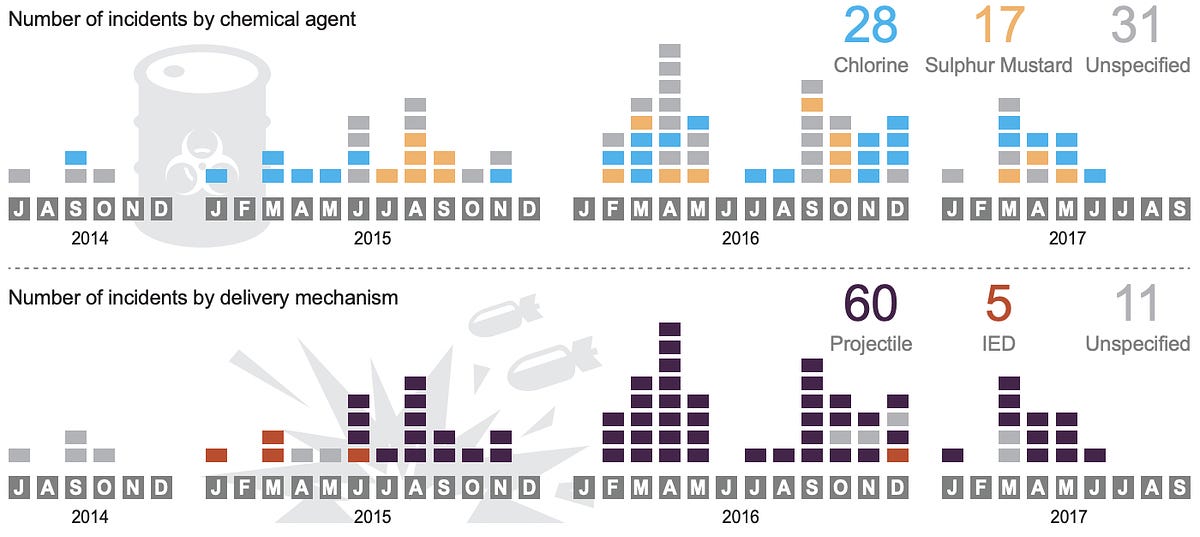
SkyLift is a zero-click Wi-Fi geolocation spoofing device that virtually relocates visitors to Julian Assange’s residence at the Ecuadorian Embassy in London. The device was made for !Mediengruppe Bitnik’s Assange room and works by broadcasting Wi-Fi signals (beacon frames) that exploit Wi-Fi geolocation services.
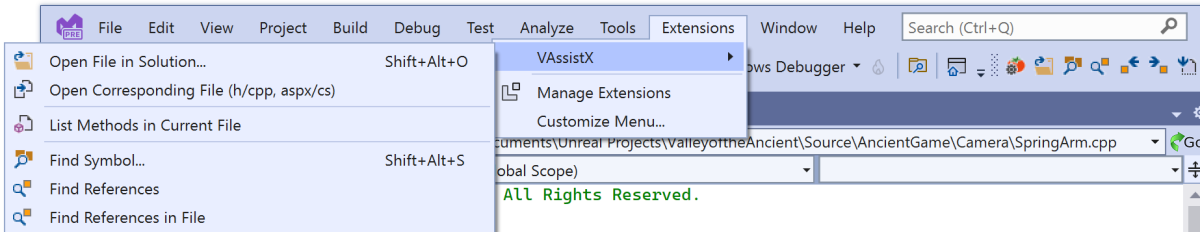
Thanks to a web-residency grant from Schloss Solitude SkyLift now runs on the ESP8266, a low-cost Arduino-compatible Wi-Fi microcontroller, and is open source. Full code and documentation on https://github.com/adamhrv/skylift.
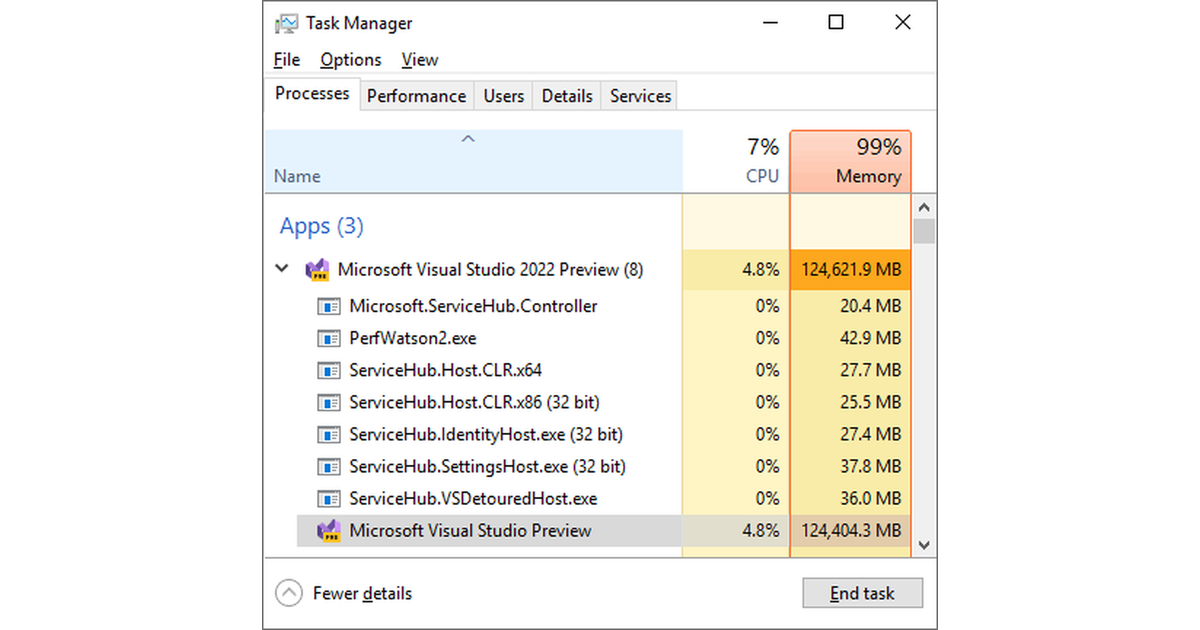
Previously, this technique would require a small linux computer, USB Wi-Fi dongles, and a program such as mdk3 to broadcast beacon frames with custom MAC addresses. This was functional but difficult to deploy and impractical. The small size and low cost of the ESP8266 microcontroller offers new possibilities for creative geolocation spoofing.
SkyLift works by broadcasting MAC addresses that are associated with Wi-Fi routers in a different location. Wi-Fi geolocation services rely on the assumed stable location of home and commercial routers to return accurate geolocation information. Because space-based GPS signals are attenuated in dense urban areas, Wi-Fi became a viable alternative for location services in consumer tech. However, it’s also vulnerable to spoofing attacks as discovered by researchers at ETH Zurich/Swiss Federal Institute of Technology all the way back in 2008.