Big Vulnerabilities in Next-Gen BIG-IP
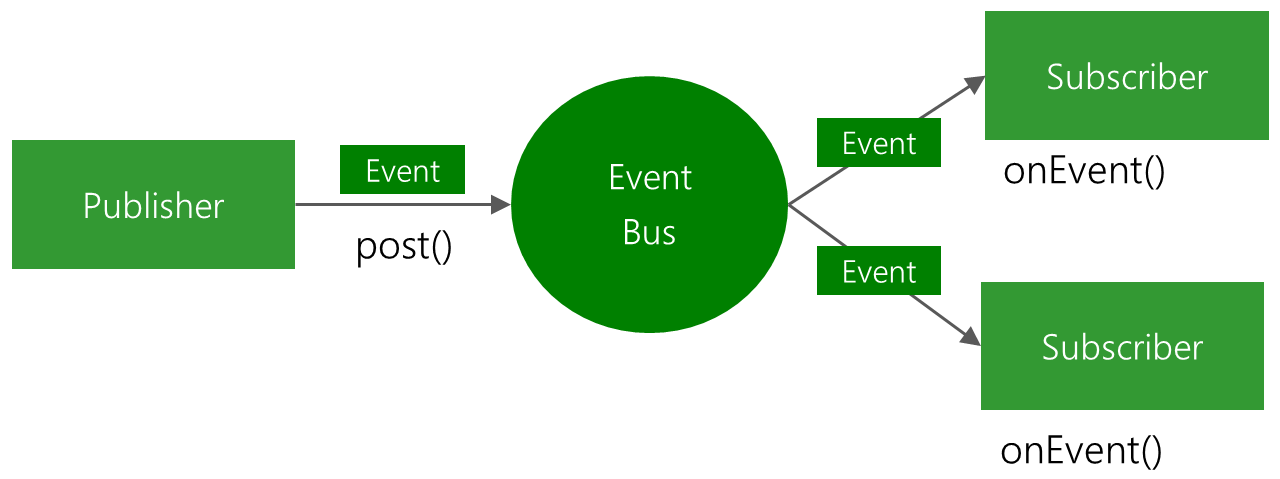
Our ongoing research has identified remotely exploitable vulnerabilities in F5’s Next Central Manager that can give attackers full administrative control of the device, and subsequently allow attackers to create accounts on any F5 assets managed by the Next Central Manager. These attacker-controlled accounts would not be visible from the Next Central Manager itself, enabling ongoing malicious persistence within the environment. At the time of writing, we have not seen any indication that these vulnerabilities have been exploited in the wild.
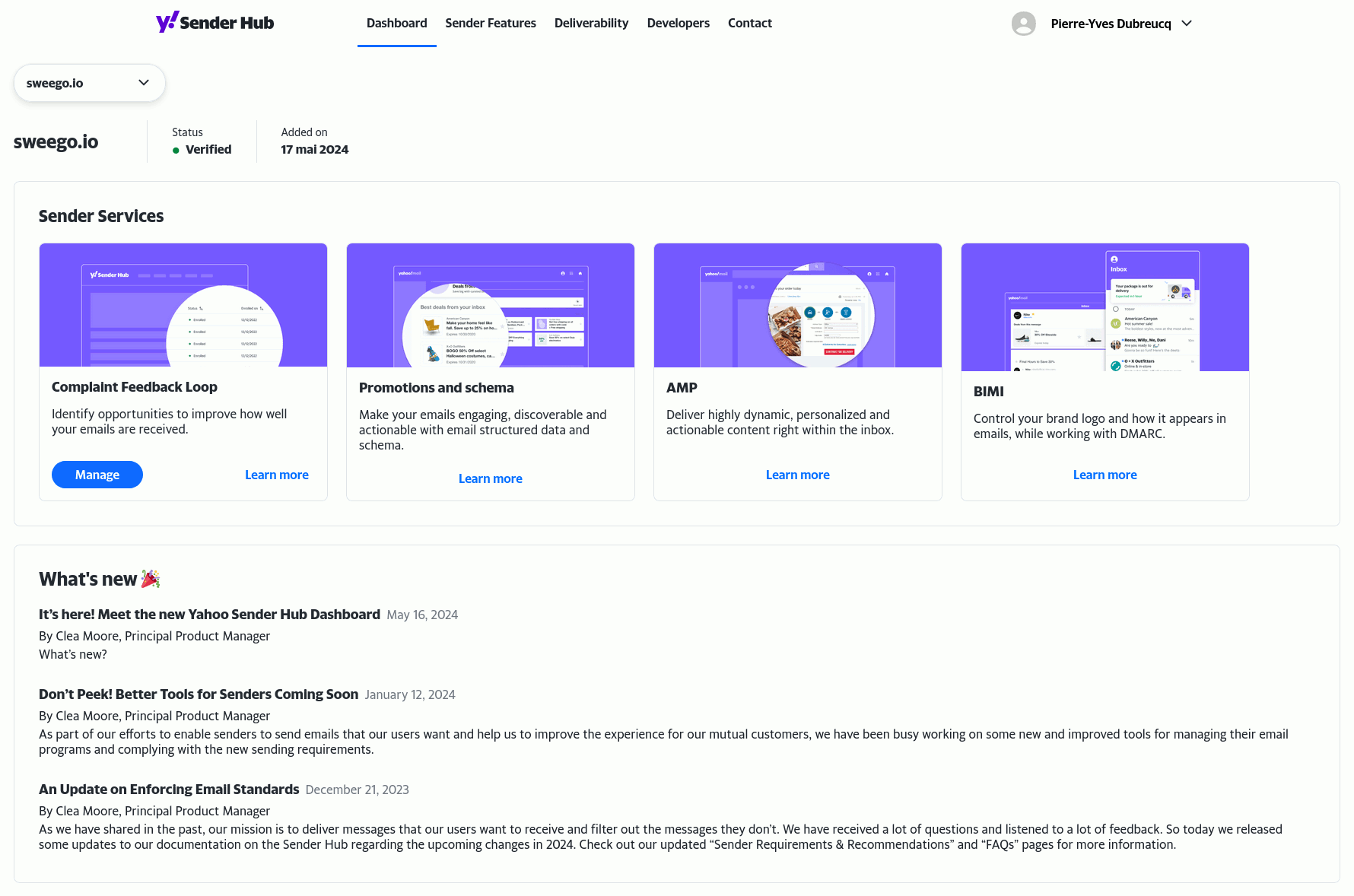
F5 has published fixes for the vulnerabilities in software version 20.2.0 available to F5 customers, here, and organizations using the Next Central Manager are advised to upgrade to the latest version as soon as possible. It is important to note that we reported 5 vulnerabilities, but only 2 CVEs were assigned, details follow below.
Networking and application infrastructure have become a key target of attackers in recent years, including a wide range of vendors such as Cisco, Citrix, Fortinet, Ivanti, and Zyxel. Exploiting these highly privileged systems can give adversaries an ideal way to gain access, spread, and maintain persistence within an environment. F5 was no exception with the 2023 discovery of a series of well-publicized vulnerabilities and attack campaigns in the wild.